CBSM: Certified Banking Security Manager

Description
Safeguarding your organization’s information is paramount for any organization. Our comprehensive Certified Banking Security Manager Certification Course is meticulously designed to provide professionals with the essential knowledge and skills to effectively manage and protect an organization’s information assets. This course empowers you to identify system vulnerabilities and develop robust strategies to counter cyber threats. You’ll learn to implement and maintain a resilient cybersecurity framework, and build, mature, and manage your information security program to meet industry-specific cybersecurity and regulatory expectations.
With over 12 hours of engaging lectures and 8 assignments based on real-life, this course will help you develop security best practices to keep customer data and sensitive information secure. Delve into critical aspects of cybersecurity, gaining insights into frameworks, incident response, business continuity, and disaster recovery!
What's Included?
- In-depth learning: 12 hours of lecture spread over 7 modules, broken down into bite-size lessons to gain a thorough understanding of cybersecurity principles.
- Practical experience: 8 highly interactive assignments based on real-life scenarios to apply your knowledge in a practical setting.
- Personalized support: Receive personal feedback and support from the instructor throughout the course to ensure your success.
- Knowledge validation: Test your understanding with 8 quizzes and a comprehensive 100-question final exam.
- GRC platform experience: During this course, you will have hands-on access to SBS's governance, risk management, and compliance software TRAC.
Covered Topics
The course content is broken down across seven modules:
- Laws and Regulations: Choosing the right cybersecurity framework, based on your needs, risks, and regulatory guidelines.
- Information Security: Building your information security plan from what to include to writing effective policy statements.
- Risk Assessments: Deep dive into how to assess and quantify risk from IT assets, vendors, business processes, and organizational risks.
- Vendor Management and Business Resilience: A through Z best practices for vendor management, and the differences between business continuity, disaster recovery, pandemic preparedness, and business resilience.
- Incident Response: Creating and testing an effective incident response plan, from components to triage and tabletop testing.
- Network Architecture and Security Awareness: Managing risk associated with different network architectures and best practices for company-wide security awareness training.
- Testing and Reporting: Best practices around testing your technology, people, and processes, and how to effectively report and track risks.
Certification
CPE Credits
 |
SBS | 12.00 |
Learning Objectives
By the end of this course, you will receive the designation of Certified Business Security Manager and have the skills to:
- Understand the fundamentals of risk management.
- Identify key business considerations in risk management.
- Explore various cybersecurity frameworks and their applications.
- Develop and implement information security policies, standards, and guidelines.
- Create a comprehensive information security plan.
- Grasp the fundamentals of business resilience.
- Apply best practices for policy statements.
- Conduct IT risk assessments effectively.
- Perform vendor risk assessments.
- Evaluate business process risks.
- Assess organizational risks.
- Manage ongoing vendor relationships.
- Plan for business continuity.
- Prepare for disaster recovery.
- Develop a pandemic preparedness plan.
- Enhance overall business resilience.
- Review and evaluate vendors regularly.
- Understand the fundamentals of incident response.
- Build a robust incident response plan.
- Identify and assess threats targeting your business.
- Conduct thorough threat assessments.
- Perform tabletop testing for incident response.
- Design secure network architectures.
- Implement effective risk mitigation strategies.
- Create and use data flow diagrams.
- Apply best practices for security awareness training.
Content
| Introduction | Module | ||
| Laws and Regulation | Module | ||
| Information Security | Module | ||
| Risk Assessments | Module | ||
| Vendor Management and Business | Module | ||
| Incident Response | Module | ||
| Network Architecture and Security Awareness | Module | ||
| Testing and Reporting | Module | ||
| Final Exam | Module |
Click here to view additional Upcoming Certification dates or if you prefer to start sooner than later, click here to start On Demand.
- Hilarie Haack, GA
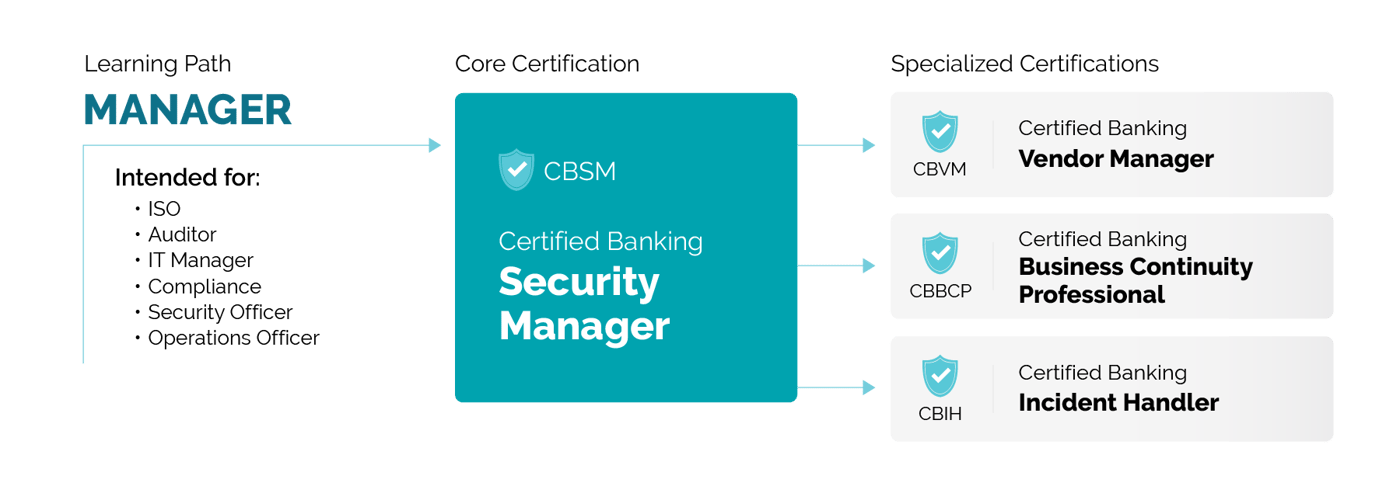
Continue your cyber education by exploring the other courses available in the Manager Learning Path: