CBSTP: Certified Banking Security Technology Professional

Description
This course will allow you to explore the technical design and implementation of Information Security Program controls.
WHAT YOU WILL LEARN:
- Incident Response Procedures
- System Hardening
- Mobile Device Management
- Penetration and Vulnerability Testing
- Patch Management
- Social Engineering Testing
- Perimeter, Network, and Endpoint Security
- Data Backup and Replication
WHO SHOULD ATTEND:
- IT Manager, Network Administrator, IT Specialist
*MUST HAVE Computer which you can install software on and do basic security testing
By purchasing this certification, you are hereby agreeing to the policies and procedures of the SBS Institute. Click HERE to read and review.
Certification
Online Certification
2024-04-02 12:00:00 UTC
- 2024-04-02 20:00:00 UTC
CPE Credits
 |
SBS | 4.00 |
Learning Objectives
- Gain a better understanding of risk management, documentation, and auditing.
- Discuss real-world cybersecurity risks and review possible technical controls and security configurations.
- Complete hands-on exercises with a variety of security testing software, such as Kali Linux.
- Gain working experience with security tools, troubleshooting and analysis tools, vulnerability scanning, and patching processes.
- Reference security standards from NIST and CIS.
Content
| Module 1: Overview of Risk Management | Module | ||
| Module 2: Active Directory and Group Policy Management | Module | ||
| Module 3: Attack Protection | Module | ||
| Module 4: Segmentation and Mobile Security | Module | ||
| Module 5: Data Backup Standards and Best Practices | Module | ||
| Module 6: Vulnerability Assessments and Patch Management | Module | ||
| Module 7: Incident Response and Detection | Module | ||
| CBSTP Final Exam | Module |
Click here to view additional Upcoming Certification dates or if you prefer to start sooner than later, click here to start On Demand.
“The course was eye-opening and valuable to my role in creating a secure environment at my company. The hands-on nature of the course and the ability to immediately apply what I learned is invaluable. I will definitely be looking into other course in the future.
- Steve Larson, WI
- Steve Larson, WI
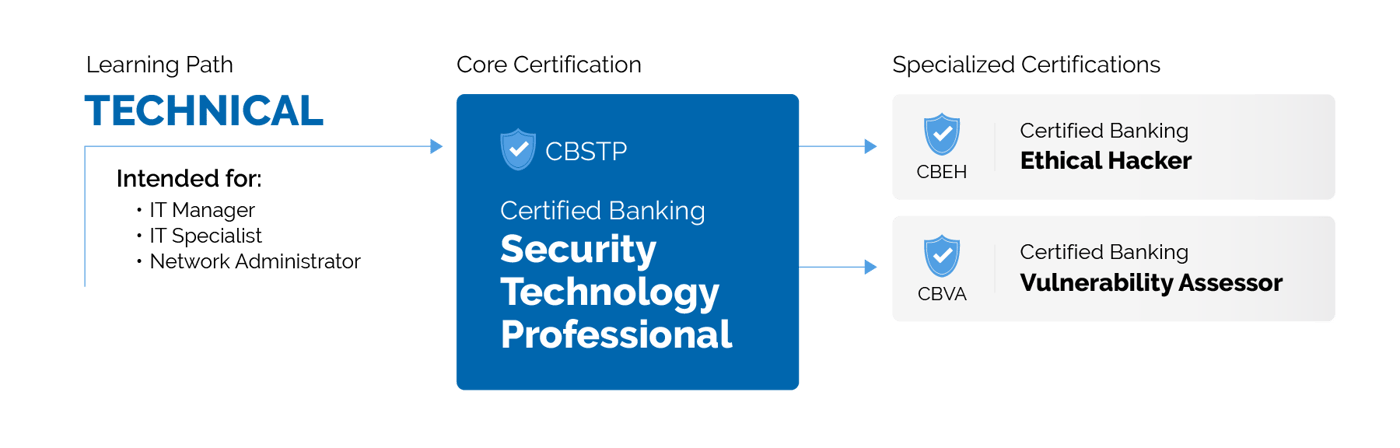
Continue your cyber education by exploring the other courses available in the Technical Learning Path: